What Option Limits the Delegation to Specific Services Running on Specific Computers?
In this article, we'll look at how to delegate administrative permissions in the Active Directory domain. Delegation allows you to grant the permissions to perform some Advertisement management tasks to common domain (non-admin) users without making them the members of the privileged domain groups, like Domain Admins, Account Operators, etc. For example, you can use delegation to grant a certain AD security grouping (say, Helpdesk) the permissions to add users to groups, create new users in AD, and reset the business relationship passwords.
Contents:
- Agreement Active Directory Delegated Permissions
- Delegate Password Reset and Unlock Account Permissions in AD
- Delegate Permissions to Join Computers to Advertizing Domain
- How to View and Remove Delegated Permissions in Active Directory?
- How to Consul Permissions in Active Directory with PowerShell?
Understanding Agile Directory Delegated Permissions
To consul permissions in AD, the Delegation of Control Wizard in Agile Directory Users and Computers (DSA.msc) is used.
You can consul authoritative privileges in AD on a fairly granular level. You can grant one group the permissions to reset passwords in the OU, another i – to create and delete user accounts, and the third one – to create and change grouping membership. Y'all can configure permission inheritance on the nested OUs. Permissions tin can be delegated in Agile Directory on the following levels:
- Advertisement site;
- The whole domain;
- A specific Organizational Unit (OU) in Active Directory;
- A specific Ad object.
Best practices for delegation command in Agile Directory:
- It is not recommended to delegate (assign) permissions directly to specific user accounts. Create a new security group in AD instead, add a user to information technology, and delegate permissions on an OU for that grouping. If you want to grant the same permissions to another user, you can simply add him to this security group;
- Avoid using Deny permissions, as they take precedence over allowed ones;
- Periodically audit the delegated permissions in the domain (a report with the current lists of permissions per OU can be created using PowerShell);
- Do not grant anyone permissions to manage the OU with the administrator accounts. Otherwise, any support staff fellow member can reset the domain administrator password. All privileged users and groups should be placed to a separate OU that is not bailiwick to delegation rules.
Delegate Password Reset and Unlock Account Permissions in AD
Let'south imagine that your task is to grant the HelpDesk group the permissions to reset passwords and unlock user accounts in the domain. Allow's create a new security group in AD using PowerShell:
New-ADGroup "HelpDesk" -path 'OU=Groups,OU=Paris,OU=Fr,dc=woshub,DC=com' -GroupScope Global
Add users y'all desire to this grouping:
Add-AdGroupMember -Identity HelpDesk -Members rdroz, jdupont
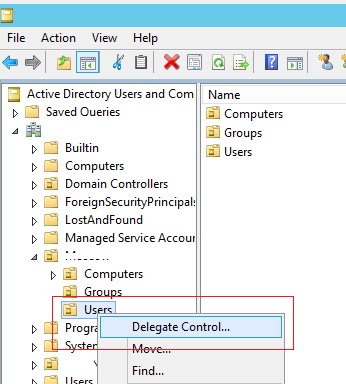
Run the Active Directory Users and Computers mmc snap-in (dsa.msc), right-click the OU with the users (in our example information technology is 'OU=Users,OU=Paris,OU=Fr,dc=woshub,DC=com'), and select the Delegate Command menu item.
Select the group you want to grant administrative privileges to.

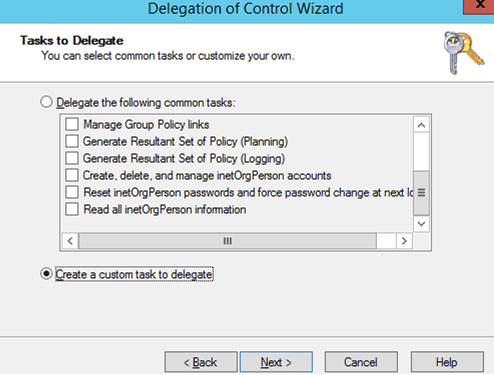
Select ane of the preconfigured set of privileges (Delegate the following common tasks):
- Create, delete, and manage user accounts;
- Reset user passwords and forcefulness password change at next logon;
- Read all user information;
- Create, delete and manage groups;
- Change the membership of a group;
- Manage Grouping Policy links;
- Generate Resultant Fix of Policy (Planning);
- Generate Resultant Set of Policy (Logging);
- Create, delete, and manage inetOrgPerson accounts;
- Reset inetOrgPerson passwords and force password alter at next logon;
- Read all inetOrgPerson information.
Or create a custom task to delegate. I choose the second option.
Select the type of AD objects you desire to grant administrative permissions to. Since nosotros desire to grant control over user accounts, select the User Object item. If y'all desire to grant the permissions to create or delete users in the OU, select the options Create/Delete selected objects in this folder. In our instance, we don't grant such privileges.

In the listing of permissions, select the ones you want to delegate. In our case, we'll select the privileges to unlock user accounts (Read lockoutTime and Write lockoutTime) and to reset a password (Reset password).
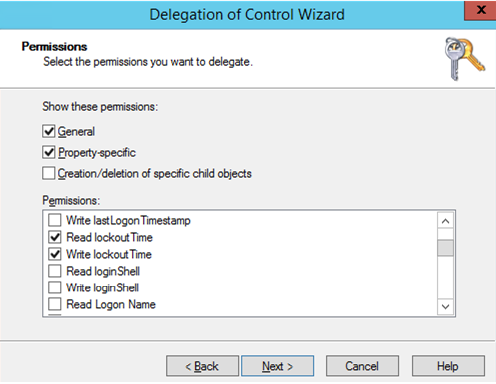
Click Side by side, and confirm the delegation of the selected permissions on the terminal screen.

Now, under a user account from the HelpDesk group endeavor to reset a password of the user from the target OU using PowerShell:
Gear up-ADAccountPassword gchaufourier -Reset -NewPassword (ConvertTo-SecureString -AsPlainText "P@ssdr0w1" -Force -Verbose) –PassThru
The password should reset successfully (if it matches the domain password policy).
Now effort to create a user in this OU using the New-ADUser cmdlet:
New-ADUser -Proper name gmicheaux -Path 'OU=Users,OU=Paris,OU=FR,DC=woshub,DC=com' -Enabled $true
An access denied fault should appear since you haven't delegated the rights to create new Advertizing accounts.
You tin use domain controller security logs to audit the actions of users to whom you have delegated administrative permissions. For example, you can track who reset a user password in the domain, who created a user account in Advertizement, or track changes in sensitive AD groups.
Delegate Permissions to Join Computers to Ad Domain
By default, any domain user can join upward to 10 computers to the domain. When adding the 11th figurer, an fault will appear:
Your calculator could not be joined to the domain. You have exceeded the maximum number of computer accounts you lot are allowed to create in this domain. Contact your system administrator to have this limit reset or increased.

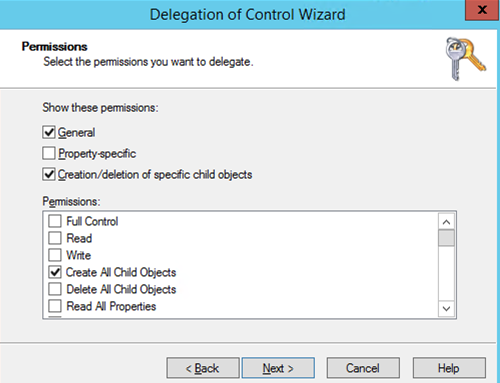
You tin alter this restriction on the domain-broad level by increasing the value of the ms-DS-MachineAccountQuota aspect. Or (which is more than right and secure) by delegating the permissions to bring together computers to a sure OU to a specific user group (helpdesk). To practice this, delegate the permissions to create objects of Figurer objects type. In the Delegation of Control Wizard, select Create selected objects in this binder.

Select Create All Child Objects in the Permissions section.
If you desire to delegate the right to movement objects between Organizational Units in AD, you must grant the following permissions: Delete User objects, Write Distinguished Name, Write name (**), Create User (or Computer) objects.
How to View and Remove Delegated Permissions in Active Directory?
Whatever number of delegation rules tin be assigned to an OU in Advertizing. Yous can become a list of groups and the permissions delegated to them in the properties of the OU in the ADUC console. Go to the Security tab.
This contains a list of AD subjects that have been granted permissions for this container. You tin see the list of granted permissions on the Advanced tab. As you can encounter, the HelpDesk group is allowed to reset passwords.
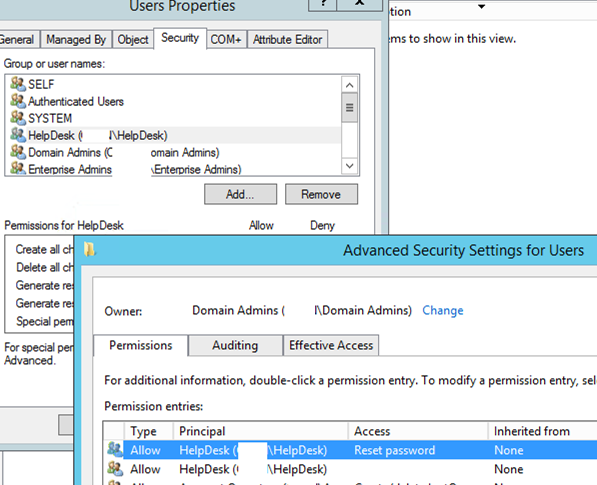
You lot tin revoke a specific group of authoritative permissions previously assigned through delegation. Find the proper noun of the group you delegated permissions to and click Remove.
In improver, on the Security -> Advanced tab you tin manually assign delegated permissions to unlike security groups.
How to Consul Permissions in Active Directory with PowerShell?
Y'all can get a list of permissions that are delegated to the OU or change the current permissions using PowerShell. The Go-ACL and Fix-ACL cmdlets are used to view and modify permissions in Active Directory (the same PowerShell cmdlets are used to manage NTFS permissions on files and folders).
The following simple script volition list all not-standard permissions that are delegated to a specific organizational unit in Advertizing:
# go the OU
$OUs = Get-ADOrganizationalUnit -Filter 'DistinguishedName -eq "OU=Users,OU=Paris,DC=woshub,DC=com"'| Select-Object -ExpandProperty DistinguishedName
$schemaIDGUID = @{}
$ErrorActionPreference = 'SilentlyContinue'
Become-ADObject -SearchBase (Get-ADRootDSE).schemaNamingContext -LDAPFilter '(schemaIDGUID=*)' -Backdrop name, schemaIDGUID |
ForEach-Object {$schemaIDGUID.add([System.GUID]$_.schemaIDGUID,$_.proper name)}
Go-ADObject -SearchBase "CN=Extended-Rights,$((Go-ADRootDSE).configurationNamingContext)" -LDAPFilter '(objectClass=controlAccessRight)' -Properties proper noun, rightsGUID |
ForEach-Object {$schemaIDGUID.add([System.GUID]$_.rightsGUID,$_.proper name)}
$ErrorActionPreference = 'Continue'
ForEach ($OU in $OUs) {
$report += Go-Acl -Path "AD:\$OU" |
Select-Object -ExpandProperty Access |
Select-Object @{name='organizationalUnit';expression={$OU}}, `
@{name='objectTypeName';expression={if ($_.objectType.ToString() -eq '00000000-0000-0000-0000-000000000000') {'All'} Else {$schemaIDGUID.Item($_.objectType)}}}, `
@{name='inheritedObjectTypeName';expression={$schemaIDGUID.Item($_.inheritedObjectType)}}, `
*
}
# study with assigned OU permissions
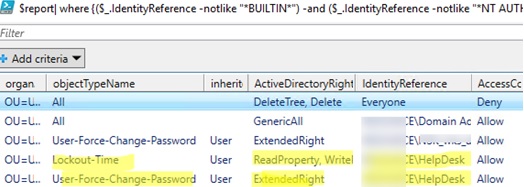
You can become the delegated permissions report with a graphical Out-GridView cmdlet:
$study| where {($_.IdentityReference -notlike "*BUILTIN*") -and ($_.IdentityReference -notlike "*NT AUTHORITY*") }| Out-GridView
Or consign the list of permissions to a CSV file for further analysis in Excel ( you tin write data directly to an Excel file from a PowerShell script):
$report | Export-Csv -Path "C:\reports\AD_OU_Permissions.csv" –NoTypeInformation
The resulting study shows that the HelpDesk grouping has been delegated the permissions to reset user passwords (ObjectTypeName=User-Strength-Change-Countersign) in the OU.
You can use the dsacls tool to consul rights to an OU. For example:
dsacls "ou=users,ou=paris,dc=woshub,dc=com" /I:Due south /G "WOSHUB\HELPDESK:CA;Reset Password;user" "WOSHUB\HELPDESK:WP;pwdLastSet;user" "WOSHUB\HELPDESK:WP;lockoutTime;user
Yous can also assign permissions to the Organizational Unit container using PowerShell (in this case, the permissions to reset the password are delegated):
$ou = "AD:\OU=users,OU=Paris,DC=woshub,DC=com"
$grouping = Go-ADGroup helpdesk
$sid = new-object System.Security.Master.SecurityIdentifier $group.SID
$ResetPassword = [GUID]"00299570-246d-11d0-a768-00aa006e0529"
$UserObjectType = "bf967aba-0de6-11d0-a285-00aa003049e2"
$ACL = go-acl $OU
$RuleResetPassword = New-Object Organization.DirectoryServices.ActiveDirectoryAccessRule ($sid, "ExtendedRight", "Allow", $ResetPassword, "Descendents", $UserObjectType)
$ACL.AddAccessRule($RuleResetPassword)
Set-Acl -Path $OU -AclObject $ACL
Similarly, you can delegate other permissions to Advert organizational containers using PowerShell.
Source: http://woshub.com/delegate-control-active-directory/
0 Response to "What Option Limits the Delegation to Specific Services Running on Specific Computers?"
Post a Comment